Vulnerable hosts can be found by scanning the Network topology for hosts outlined in orange, reviewing their vulnerability scores, or searching for the vulnerability tag in either the Network or Inventory tab.
Finding Vulnerable Hosts in the Network
Using Tags
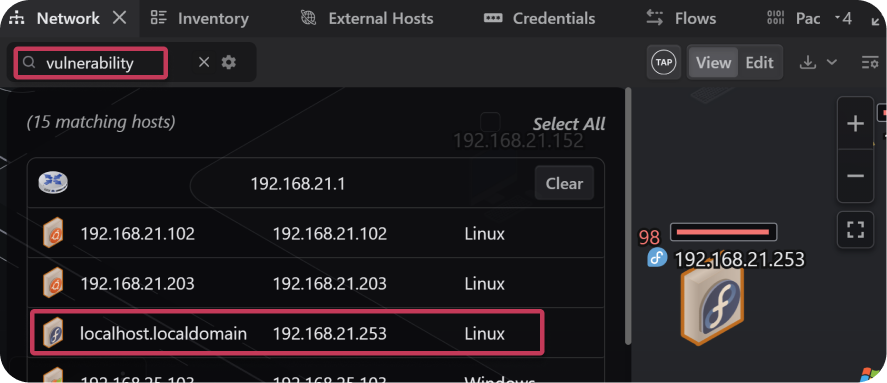
- Open the Network tab and search for the
vulnerabilitykeyword. - The Network topology dims all hosts that do not match the search.
- Select a host from the search results to locate it in the topology.
- Click the host to display details in the Inspector, including identified CVEs.
Using Vulnerability Score and Color
Each host in the Network panel is assigned a vulnerability score based on identified CVEs and vulnerability scanners. Hosts with detected vulnerabilities are also outlined in orange.
Enabling Vulnerability Scoring
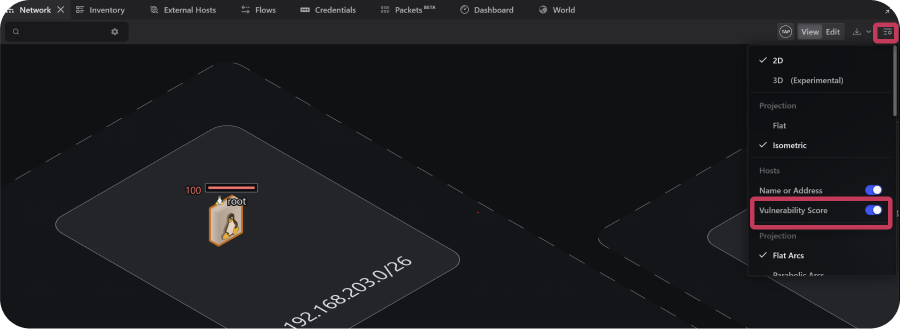
- Open the Network panel.
- Select the Network View Settings icon.
- Enable Vulnerability Score from the dropdown.
Finding Vulnerable Hosts in the Inventory
Open the Inventory tab and search for the Vulnerability tag. All hosts with this tag are displayed, while hosts without it are temporarily hidden.
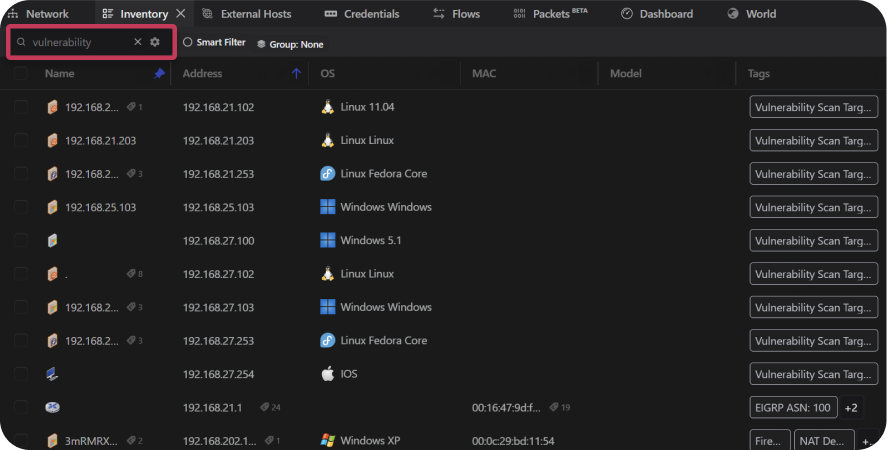
Note: Searching by vulnerability score or the orange outline is recommended, since not all vulnerable hosts may be tagged.